/home/puc4zdn0hvjg/public_html/suniteditconsultants.com/wp-content/plugins/rselements/widgets/heading/heading.php on line 516
">
">
NEED HELP ?
Let us know what your IT needs are and our experts will provide you a quote.
info@uniteditconsultants.com
Secure your digital frontier with our Cyber Security Services.
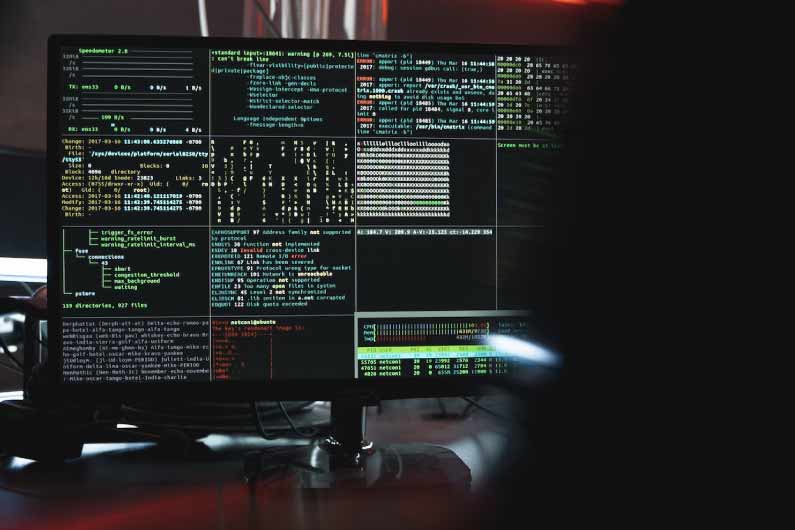
Prevent data breaches before they happen with comprehensive security services, part of the suite from UIC. The certified engineers at our US-based Security Operations Center provide real-time visibility and around-the-clock protection against current threats, as well as emerging attack strains appearing daily.
Fortify your defenses with 24/7/365 security information and event monitoring (SIEM) from UITC. Our certified engineers hold PCI, SOC 2, and HIPAA compliance certifications, ensuring real-time visibility, intelligent analysis, and threat monitoring for your entire IT infrastructure.
Your guide to a better digital future
We offer our customers a variety of cybersecurity services to:

Security infrastructure design and management
Vulnerability management.
Managed detection and response.
Compliance management.

IT security consulting.
Comprehensive security assessments: e.g., to evaluate all aspects of medical device security.
Security testing of apps and IT infrastructures.
Stress testing: emulation of DDoS / DoS attacks.

Security code review.
Mobile device management and mobile application management.
Cloud security.
Web application security.

SIEM.
DDoS protection.
Email security.
Firewalls, IDS / IPS, DLP implementation and setting.
Antivirus protection.
We continuously run cyber assessments to help identify threats and prioritize a prevention strategy or action plan. This helps us design and integrate advanced cybersecurity programs and measures to assist you in proactive network threat detection and immediate response to any possible breach. A Zero Trust Cybersecurity strategy assumes compromise and sets up controls to confirm every user, device, and connection into the business for authenticity and purpose.

